The Cyberfores SOC Lab defends a fictional enterprise designed to resemble a small-to-mid-size organization.
The simulated organization includes:
Active Directory users, groups, and policies
Employee workstations generating normal business activity
Internal servers hosting business services
Authentication, access, and file activity logs
Segmented network zones to replicate enterprise traffic flow
This approach ensures security events always have business context, mirroring what analysts experience in real SOC environments.
Simulated Company profile
Company : Oromil LLC
Oromil (Simulated Environment) represents a growing consumer goods and e-commerce organization focused on home organization products. This environment is intentionally designed to reflect the structure, workflows, and risks of a real small-to-mid-size business operating with a combination of on-site infrastructure and remote employees.
All activity within this environment is generated for security testing and educational purposes.
Industry
Consumer Goods
E-commerce
Home Organization Products
This industry profile reflects a common SMB threat landscape involving customer data, financial operations, logistics systems, and remote workforce access.
Organization Size
Employees: 25
Locations: Lousville,KY with remote workers
IT Maturity: Early-stage to moderate enterprise infrastructure
This scale mirrors organizations frequently supported by internal security teams or managed SOC providers.
Business Departments
The simulated organization includes multiple departments to generate realistic identity, access, and activity patterns across the environment:
Human Resources
Sales
IT & Systems Administration
Departmental separation enables testing of role-based access controls, privilege boundaries, and department-specific threat scenarios.
Employee & Account Types
The environment includes multiple user and account personas to support varied authentication and activity patterns:
Standard office employees (domain users)
Remote workers (VPN-enabled access)
IT administrators (privileged accounts)
Service accounts supporting internal systems
This structure enables realistic generation of authentication logs, access events, and privilege-related alerts.
Critical Business Assets
The simulated Oromil environment protects high-value assets commonly targeted in SMB environments:
Active Directory domain services
Internal file storage and document repositories
Finance and operations systems
Employee workstations and laptops
Internal application and service servers
These assets serve as detection points for credential abuse, lateral movement, and unauthorized access scenarios.
Threat & Risk Context
As a growing e-commerce and consumer goods organization, Oromil represents a realistic target for modern cyber threats, including:
Phishing and credential theft
Privilege escalation and lateral movement
Insider threat activity
Ransomware and data extortion scenarios
Unauthorized access via remote services
This threat profile allows the SOC Lab to simulate and analyze attacks commonly faced by real-world organizations.
Purpose of This Environment
The purpose of the simulated Oromil environment is to ensure that all security detections, investigations, and response workflows are performed with clear business context, closely mirroring how analysts operate in real SOC environments.
Rather than focusing solely on individual tools, the CyberFores SOC Lab emphasizes understanding who was affected, what systems were involved, and why the event matters to the business.
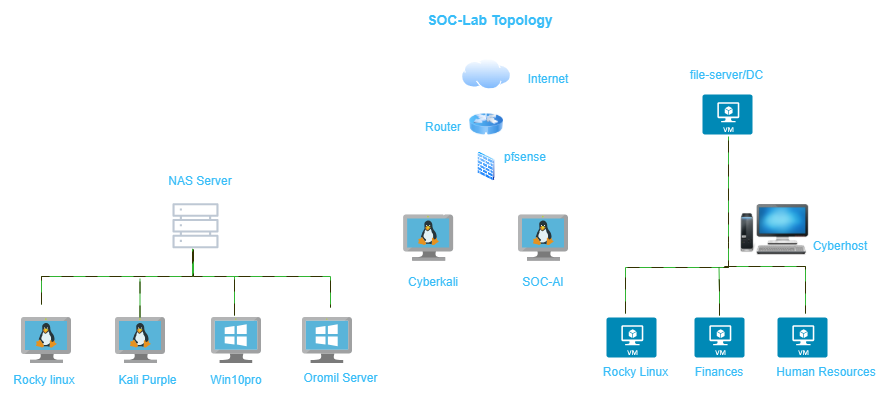
Relationship to the SOC Lab Infrastructure
The simulated business environment directly informs how each virtual machine and network segment is designed and monitored:
Identity systems generate authentication and access events
Employee endpoints produce endpoint and behavioral telemetry
Servers host services tied to business operations
Attack simulations are mapped to realistic business impact
This approach transforms the SOC Lab from a collection of tools into a structured, enterprise-aligned defensive environment.
Disclosure
This site documents a simulated enterprise environment built for professional development, security testing, and portfolio demonstration.
No real customer data, production systems, or live business operations are exposed.